Crypto Ledger Phishing Protection: Defense Against Scams
Identify fake software and protect your crypto from phishing and malware.
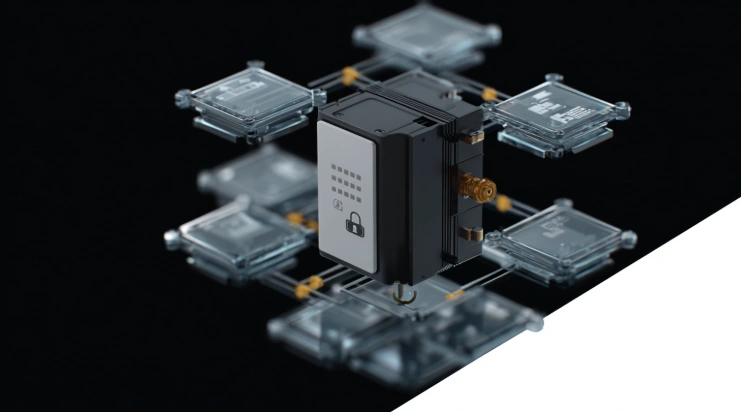
Crypto Ledger Phishing Protection encompasses multiple security layers designed to defend users against fraudulent software, fake websites, and social engineering attacks. Phishing represents one of the most common attack vectors in cryptocurrency theft, with attackers creating convincing replicas of legitimate applications to capture recovery phrases or redirect transactions. Understanding these threats and the protective mechanisms available is essential for secure hardware wallet usage.
Crypto Ledger scam protection operates through both technical measures and user awareness. The hardware wallet architecture inherently resists many phishing techniques because private keys cannot be extracted even by malicious software. However, users must still recognize and avoid attacks that attempt to trick them into revealing recovery phrases or approving fraudulent transactions.
Protection Against Phishing and Fake Apps
Crypto Ledger phishing protection begins with the application distribution model. Official software is available only through verified channels: ledger.com for desktop applications and official app stores (Apple App Store, Google Play Store) for mobile versions. Each release is cryptographically signed, enabling verification of authenticity before installation.
The hardware wallet itself provides additional phishing resistance through:
- Independent transaction display on the hardware screen that malware cannot modify
- Genuine check verification confirming device authenticity with Ledger servers
- Physical confirmation requirement for all transactions, preventing automated theft
- Recovery phrase display only on hardware screen, preventing capture by fake software
These mechanisms ensure that even if a user accidentally installs fraudulent companion software, the attacker cannot steal assets without physical access to the hardware wallet and PIN knowledge.
How to Identify Fake Crypto Ledger Software
Fake Crypto Ledger app identification requires attention to several key indicators:
- URL verification: The download must originate from exactly ledger.com (desktop) or verified app store listings (mobile). Similar domains like ledger-live.com, ledgerapp.io, or ledger-download.net are fraudulent.
- Publisher verification: Mobile apps must show "Ledger SAS" as the publisher. Desktop installers should display valid Ledger SAS certificates during installation.
- Recovery phrase requests: Legitimate software never asks for the 24-word recovery phrase on a computer or phone screen. Any prompt for complete phrase entry indicates malware.
- Browser extensions: Ledger does not distribute wallet management browser extensions. Any extension claiming to be Crypto Ledger or Ledger Live is fraudulent.
- Unsolicited communications: Ledger does not send download links via email or social media. Official communications direct users to navigate to the website independently.
Common Phishing Attack Methods
Crypto Ledger scam protection requires understanding the attack methods criminals employ:
| Attack Method | How It Works | Warning Signs |
|---|---|---|
| Fake websites | Clone sites on similar domains hosting trojanized downloads | URL does not match ledger.com exactly |
| Search engine ads | Paid advertisements outranking official results | "Sponsored" label, non-official URL |
| Email phishing | Messages claiming urgent security updates requiring download | Download links in email, urgency language |
| Social media scams | Posts offering support or giveaways with malicious links | DMs from unofficial accounts, too-good offers |
| Fake mobile apps | Counterfeit apps in unofficial stores or sideloaded APKs | Different publisher, third-party app stores |
| Support impersonation | Scammers posing as Ledger support requesting phrases | Requests for recovery phrase or remote access |
| Fake browser extensions | Extensions claiming wallet functionality | Any Ledger wallet browser extension |
Email and Social Media Scams
Crypto Ledger phishing protection must address email and social media attacks, which are among the most common vectors:
Email scams typically: claim security breaches requiring immediate action; contain links to fake download pages or phishing sites; request verification of account details or recovery phrases; mimic Ledger branding with slight variations; create urgency through threats of account suspension.
Social media scams typically: pose as official Ledger accounts with similar names; offer customer support through direct messages; promote fake giveaways requiring wallet connection; share malicious links in comments on legitimate posts; target users who publicly discuss Ledger products.
Legitimate Ledger communications never request recovery phrases, never include direct download links, and never threaten account suspension (hardware wallets have no accounts to suspend).
Hardware Wallet Defense Against Malware

Crypto Ledger phishing protection includes inherent resistance to malware through hardware architecture:
- Private keys cannot be extracted because they exist only inside the tamper-resistant secure element.
- Transaction details display on the hardware screen independently of the potentially compromised host device.
- Physical button presses or touchscreen confirmation required for all transactions prevents automated theft.
- Recovery phrases never appear on computer or phone screens during normal operation.
- Firmware verification ensures only signed code executes on the hardware wallet.
Even sophisticated malware with complete control over the host computer cannot: access private keys stored in the secure element; modify transaction details shown on the hardware screen; approve transactions without user physical confirmation; capture recovery phrases that display only on hardware.
The primary remaining attack vector is social engineering that tricks users into voluntarily revealing recovery phrases or approving fraudulent transactions shown on the hardware screen.
Verification Checklist for Safe Usage
Crypto Ledger scam protection through user practices:
- Always type ledger.com directly in the browser address bar. Never click links from emails, advertisements, or social media posts.
- Verify HTTPS connection and certificate validity before downloading any software.
- Check publisher certificates during installation (Ledger SAS on all platforms).
- Confirm mobile app publisher shows "Ledger SAS" in app store listings.
- Never enter the 24-word recovery phrase on any computer, phone, or website.
- Always verify transaction details on the hardware wallet screen before confirming.
- Compare recipient addresses character by character on the hardware display.
- Ignore all unsolicited messages claiming to be Ledger support.
- Report phishing attempts through the official Ledger support portal.
- Keep both hardware firmware and companion app updated to latest versions.
For private key protection details, see our Crypto Ledger Private Keys guide. For overall safety assessment, visit Is Crypto Ledger Safe.
Frequently Asked Questions
-
Immediately create a new wallet on the hardware device with a fresh recovery phrase and transfer all assets to the new accounts. Consider the old phrase permanently compromised.
-
The genuine check during setup verifies hardware authenticity but cannot directly verify companion software. Users must verify downloads originate from official sources.
-
Attackers pay for advertisements that can outrank organic results. Always skip sponsored listings and navigate directly to ledger.com.
-
Never. Legitimate Ledger software, support staff, and communications will never request the complete recovery phrase. Any such request is fraudulent.
-
Check the sender domain matches exactly @ledger.com. However, even legitimate-looking emails should not be trusted for downloads. Navigate to the website directly.
-
The transaction has likely executed if confirmed. In the future, always verify recipient address and amount on the hardware screen before physical confirmation.
-
Counterfeit devices have been distributed through unauthorized sellers. Purchase only from ledger.com or authorized resellers. The genuine check verifies device authenticity.